How Do Hackers Use Excel Files to Compromise Your Computers?
Official Team May 02, 2019 16:00
We do not recommend users to open excel (especially excel files among other office format files) from an unknown source. Hacker can gain full control of your computer, including the access of all files, screenshots, your web camera and all information typed by your keyboard!

Following the article titled "Beware of Excel Files in Email Attachment, Says Symantec", some of our readers are curious about how hackers use excel files to compromise user’s computers. Below is a simple tutorial for you.
We do not recommend users to open excel (especially excel files among other office format files) from an unknown source. Hacker can gain full control of your computer, including the accessibility of all files, screenshots, your web camera and all information typed by your keyboard.
How hackers do it?
Answer: Visual Basic Application (VBA) in excel
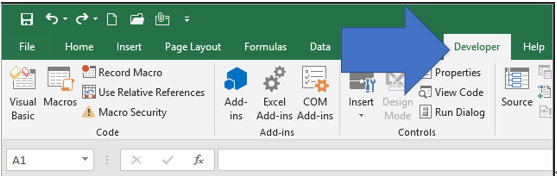
After you enable the "developer" feature in Microsoft Excel, you can click into "Visual Basic" to code anything on it.
Hacker first injects VBA codes to excel so that every time the excel is opened (P.S. We are not going to provide the codes), the victim's computer will initiate a connection towards the hacker's machine (so he needs to inject an IP address to the code). Then the hacker attaches the excel with a fancy email subject to victims.
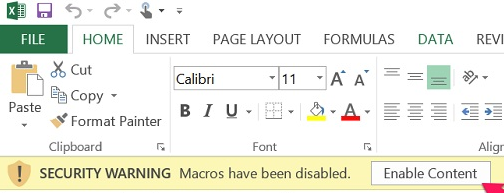
When the victim opens the excel file and "CLICK ENABLE CONTENT", his computer will be compromised.